Join the live Microsoft Partner webinar on June 11 to see the blueprint in action. Learn More
-
Offers
FIXED PRICE · 5 DAYS
Delivery Blueprint
Architecture map, prioritized backlog, 15/20/45 plan, and risk register — ready for your board.
- Architecture decision record
- Sprint-ready backlog
- Risk register with mitigations
FIXED SCOPE · 15 DAYSAutomation Sprint
One workflow shipped end-to-end with audit trail, monitoring, and full handover to your team.
- Process audit + automation map
- Working automation in production
- Monitoring + handover docs
RESCUE · 2 WEEKSProject Rescue
Stabilize a stalled project, identify root causes, reset delivery, and build a credible launch path.
- Root-cause analysis report
- Stabilized codebase + CI/CD
- Revised delivery roadmap
RETAINER · ONGOINGIntegration Reliability
Monitoring baseline, incident cadence targets, and ongoing reliability improvements for your integrations.
- Monitoring + alerting setup
- Monthly reliability report
- Priority incident response
Not sure which offer?
Answer 3 quick questions and we'll recommend the right starting point for your project.
Choose your path → -
Services
Business Intelligence Consulting
Turn scattered data into dashboards your team actually uses. Weekly reporting, KPI tracking, data governance.
Power BI · Azure Data · ETL pipelinesAzure Development
Cloud-native apps, APIs, and infrastructure on Azure. Built for scale, maintained for reliability.
↳ Azure Application DevelopmentPower Platform Development
Automate manual processes and build internal tools without the overhead of custom code. Power Apps, Power Automate, Power BI.
Power Apps · Power Automate · DataverseDynamics 365 CRM
Sales pipelines, customer data, and service workflows in one place. Configured for how your team actually works.
Sales · Service · Marketing · Field ServiceBespoke Software Solution
Custom .NET/Azure applications built for workflows that off-the-shelf tools can't handle. Your logic, your rules.
.NET · Azure · SQL Server · REST APIsStart with a Blueprint
Every engagement starts with a clear plan. In 10 days you get:
- Architecture decision record
- Prioritized backlog
- 30/60/90-day plan
- Risk register
-
Industries
Healthcare & Compliance
Patient data systems, compliance reporting, and workflow automation for regulated environments.
- HIPAA-aware integration pipelines
- Automated compliance dashboards
- Patient workflow digitization
Logistics & Supply Chain
Real-time tracking, route optimization, and inventory visibility across your distribution network.
- ERP/WMS integration
- Automated dispatch workflows
- Supply chain dashboards
SaaS & Tech-enabled
Scale your product infrastructure, integrate third-party tools, and ship features faster with reliable ops.
- API-first architecture
- Multi-tenant infrastructure
- CI/CD and release pipelines
Banking & Financial
Secure transaction processing, regulatory reporting, and customer-facing portals for financial services.
- Regulatory reporting automation
- Secure data integration
- Customer portal modernization
- Case Studies
Featured Case Studies
Browse all case studies →Euro Truck ServiceLogistics firm automated 12 manual workflows in a single 30-day sprint
"Read case study →Ergonnex AI 360Ergonnex AI 360 is a powerful project management platform that helps IT companies manage their projects better with built-in AI-powered analytics
Read case study →PanoramikPanoramic caters to your passion for sharing photos in a social media environment.
Read case study →Start your own success story
Get a clear plan in 10 days. No guesswork, no long proposals.
See case studies →- Resources
PROOF & ASSETSLEARNDelivery Blueprint Checklist
Download our free checklist covering the 10 steps to a successful delivery blueprint.
Download free →- Company
Talk to an architect
15-minute call with a solutions architect. No sales pitch — just clarity on your project.
Book a call →
Home » Identity and Access Management What Teams Often Get Wrong
Identity and Access Management What Teams Often Get Wrong

Rohit Dabra
Introduction
Many enterprise teams treat identity and access as if they are the same thing. They aren’t. Identity confirms who a user is. Access defines what that user is allowed to do. Assuming that an authenticated identity automatically deserves access is one of the most common—and costly organizational security mistakes.
Flexible work environments, remote access, and after-hours system use have made this problem worse. Even with identity and access management (IAM) programs in place, enterprises often grant too much access that later result into financial losses.
Gartner has repeatedly highlighted that breaches frequently occur not because identities are missing, but because access is poorly governed.
This blog discusses the major gaps in an organization’s IAM security and how correcting identity vs access management misunderstanding strengthens enterprise security.
Identity Management vs Access Management – The Core Difference
In most organizations, identity and access are often treated as the same thing, but they answer two very different questions. Teams often assume that once someone is verified, they can be trusted with everything related to their role. Which is not true.
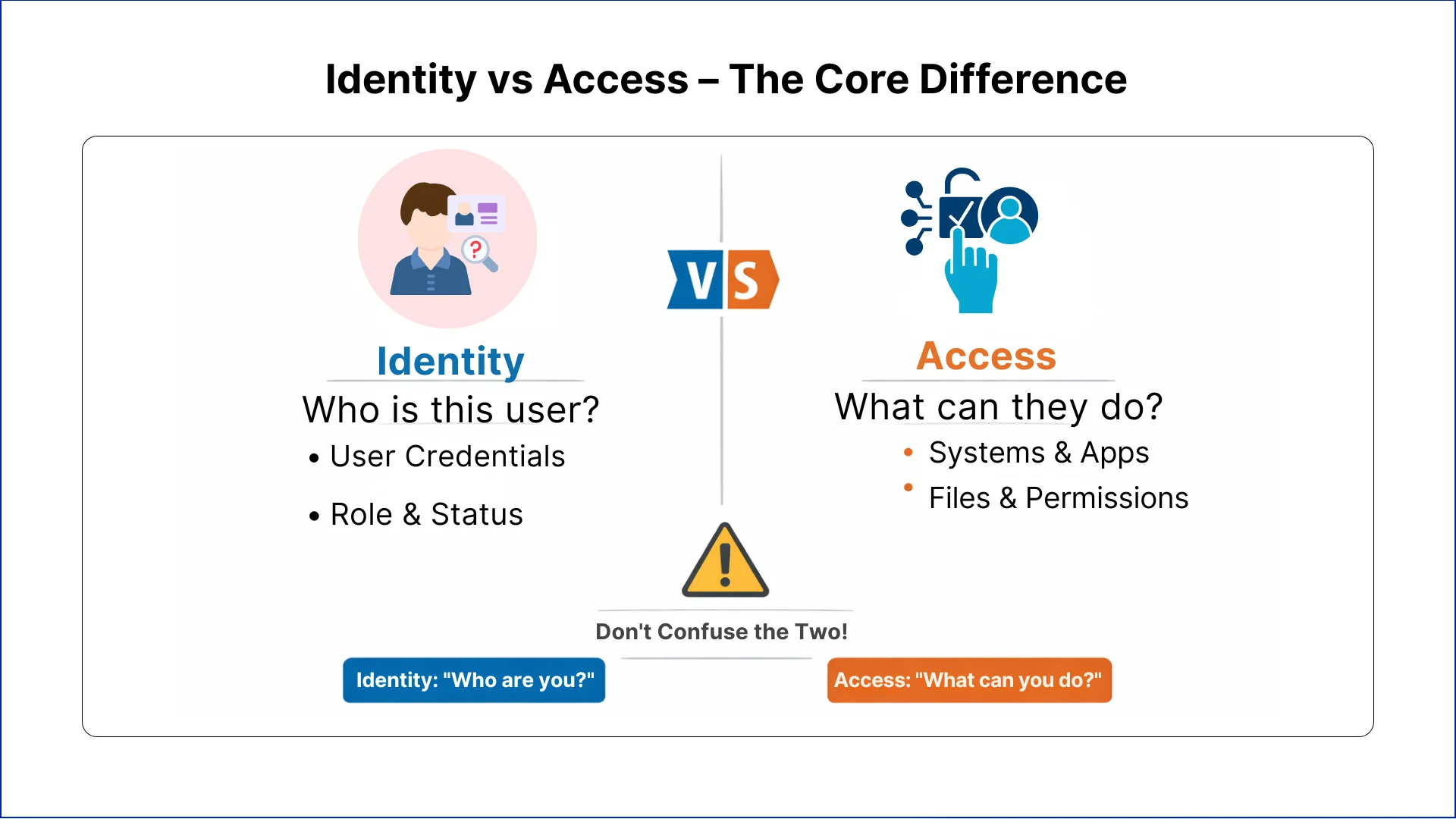
Access answers the question: What is this person allowed to do? It defines which systems, files, and functions the person can use.
Identity management security focuses on making sure the right people are correctly identified. Access management ensures they only do what they need to do. Confusing these two leads to errors that are often invisible until something goes wrong.
Let's Discuss Your Project
Get free Consultation and let us know your project idea to turn into an amazing digital product.
Six Major Blunders Enterprises Make with IAM Security
Even organizations with strong IAM programs often make simple mistakes. These mistakes are usually about processes, not technology.
Mistake 1: Giving Extra Access
To speed up onboarding or reduce internal requests, many teams grant broader access than necessary. The thinking is practical. It avoids delays and future approvals.
Over time, this practice creates users who can:
- View systems they never use
- Access data outside their responsibilities
- Perform actions they were never meant to perform
IAM security suffers when access is given for convenience rather than actual need. What starts as a time-saving step becomes a long-term problem.
Mistake 2: Not Removing Access When Roles Change
Employees move between teams, get promoted, or take temporary assignments. Many enterprises add new access but forget to remove old permissions.
This leads to:
- Users holding access to multiple departments
- Old systems still available to employees who no longer need them
- Higher risk if accounts are misused or accessed by attackers
Identity may remain correct, but access no longer reflects what the person should be able to do. This mismatch is one of the most persistent IAM mistakes enterprises make.
Mistake 3: Contractors Treated Like Employees
Temporary workers and contractors often receive the same access as permanent staff. When contracts end, accounts may remain active.
This allows:
- Former contractors to continue accessing systems
- Sensitive data to be exposed outside the organization
- Compliance gaps that auditors notice
Treating temporary staff like permanent employees is one of the easiest ways IAM security fails.
Mistake 4: Trusting Roles Instead of Checking Access
Some teams assume that if a person has a senior position or long tenure, they can be trusted with broad access. This is common but risky.
The result is:
- Users having permissions they do not need
- Role changes not reflected in access
- Accumulation of unnecessary permissions over time
Access should be based on actual responsibilities, not assumed from a job title.
Mistake 5: Access is Removed Late After Employee Exit
When employees leave, removing access is often delayed. Accounts may remain active for days or weeks because of slow processes.
This exposes the organization to:
- Former employees accessing email or systems
- Sensitive information being at risk
- Audit and compliance issues
IAM compliance expects access to be removed immediately when someone leaves.
Mistake 6: IAM Seen as an IT-Only Responsibility
IAM is often owned only by IT. Business teams, HR, and security teams are frequently not involved.
This creates problems like:
- Access decisions made without business context
- Slow response to changes
- Lack of accountability during audits
IAM works best when multiple teams share responsibility. Identity and access management is not only technical; it is operational.
How These Mistakes Affect Security and Compliance
When identity or access management are managed incorrectly, the consequences may not be immediately visible, but they build up over time.
Security Impact
- Users retain permissions they don’t need, increasing internal risk
- Old accounts remain active, giving attackers more targets
- Breaches happen not because identities are missing, but because access is uncontrolled
Compliance Impact
- Regulated industries require clear access control
- Delays in revoking access or improper assignment trigger audit findings
- Poor IAM security leads to remediation work, fines, or reputational risk
Treating identity and access as the same makes both security and compliance harder to manage.
Eager to discuss about your project ?
Share your project idea with us. Together, we’ll transform your vision into an exceptional digital product!

The Key to Effective IAM Security for Enterprise Teams
Effective IAM security comes from actively managing identity and access in a way that reflects actual work responsibilities. It is not about installing tools; it is about aligning access with real business needs.
1. Align Access with Real Responsibilities
Each user’s access should match their role. Employees should only have permissions for the systems and data they need. Granting extra access for convenience or future needs increases risk and creates hidden security problems. Access should change as responsibilities change, ensuring identity and access are always aligned.
2. Review Access Regularly
Access must be reviewed at regular intervals. These reviews ensure that permissions still match work responsibilities. Managers, system owners, and security teams should verify that access is appropriate and remove anything unnecessary. Regular reviews prevent access from accumulating over time, keeping IAM security effective.
3. Remove Access Immediately When Not Needed
When employees leave, change roles, or finish temporary assignments, access should be revoked right away. Delayed removal leaves systems exposed and increases the risk of unauthorized activity. Immediate removal simplifies compliance and keeps enterprise systems secure.
4. Handle Privileged Access Separately
High-level permissions require special attention. Administrative accounts should be granted only, when necessary, monitored regularly, and reviewed separately from standard accounts. Treating privileged access the same as regular access increases exposure and complicates audits.
5. Make IAM a Shared Responsibility
IAM security should involve IT, business leaders, HR, and security teams. Shared responsibility ensures that access decisions consider business context, role changes are captured correctly, and accountability is clear. Collaboration improves speed, accuracy, and compliance.
6. Support Zero Trust Practices
Zero trust assumes no one should have access by default. IAM security should check and approve access continuously, monitor changes, and prevent unnecessary permissions. Correctly managed IAM supports zero trust without slowing operations, giving organizations control over who can do what.
Conclusion
In regulated environments, simply knowing who someone is does not guarantee security. Identity management without proper access controls leaves organizations exposed to risks such as over-privileged accounts, insider threats, and compliance failures.
Teams must focus on both identity and access management, ensuring that users have the right permissions for their roles at all times.
When identity and access management is handled correctly, employees see only what they need, sensitive systems remain secure, and compliance requirements are consistently met. IAM security becomes a strength, not a risk, giving teams confidence that their organization is safe.
Frequently
Asked Questions
What is identity and access management?
IAM is a security framework that verifies user identities and controls their system permissions. It ensures the right people access appropriate resources at the right time, protecting sensitive data through authentication and authorization controls.
Is identity management the same as access management?
No, they serve distinct functions. Identity management confirms who users are through authentication, while access management determines what they can do through authorization. Both components work together within IAM security frameworks.
What's the core difference between identity and access management?
Identity management validates user credentials and maintains user profiles. Access management enforces permissions based on roles and responsibilities. Identity answers “who are you” while access controls “what can you do.”
How do identity and access management work together?
Identity management authenticates users first, then access management applies authorization rules. This sequential process ensures verified identities receive appropriate permissions, creating layered security that prevents unauthorized actions even from authenticated users.
Do you need identity management without access management?
No, authentication alone creates security gaps. Verified identities without controlled permissions lead to over-privileged accounts and compliance failures. Effective IAM requires both components to enforce least privilege and protect enterprise resources.
What happens when former employees retain system access?
Delayed access revocation creates security vulnerabilities and compliance violations. Former employees can leak sensitive data, access confidential systems, or compromise accounts. Immediate deprovisioning upon termination prevents unauthorized access and audit findings.
How does privileged access management differ from IAM?
PAM specifically controls high-level administrative permissions requiring extra security measures like session recording and just-in-time access. IAM governs standard user permissions across the organization, while PAM adds specialized controls for elevated privileges.
Why do contractors need different access controls?
Contractors have temporary relationships requiring time-bound permissions and stricter monitoring. Unlike employees, their access should automatically expire with contract end dates, preventing persistent accounts that create compliance gaps and security risks.
What role does IAM play in zero trust security?
IAM enforces continuous verification and least privilege access central to zero trust architecture. It validates every access request regardless of network location, monitors behaviour patterns, and revokes permissions dynamically based on risk signals.
How often should organizations review user access?
Quarterly reviews catch permission creep before it becomes problematic. High-risk accounts need monthly audits, while privileged access requires continuous monitoring. Regular reviews ensure permissions align with current responsibilities and prevent unauthorized access accumulation.

Do you have more questions?
Have a one on one discussion with our Expert Panel
Related Topics
Choosing the right business intelligence platform is one of the highest-leverage decisions a data team makes, and power bi consulting services exist precisely because that choice carries years of cost and lock-in. Power BI, Tableau, and Looker each win in different scenarios, and the honest

Choosing a business intelligence platform is one of the most consequential decisions a data team makes, and power bi consulting services exist precisely because that choice rarely comes down to features alone. Power BI, Tableau, and Looker each win in different environments, and the right

Choosing dynamics 365 consulting services is rarely about the software itself, it's about the gap between what Microsoft sells and what your business actually runs on. Most mid-to-enterprise teams on the Microsoft stack already know D365 can handle their CRM, finance, and operations. The hard

Founder and CEO

Chief Sales Officer
Talk To Sales

Get Your Free
Technical Estimate
Share your project details and
receive a detailed roadmap, timeline, and
infrastructure plan within 10-15 mins.